Introduction To Internet Hoaxes
In this modern age, the Internet has offered us immense benefits and advantages, starting from seamless communications and connectivity.
The Internet has become an integral part of our lives; we can only imagine our day-to-day activities without the use of Internet.
The Internet is full of oceans of wealth, with some significant drawbacks due to nuisances like internet hoaxes, cyber bullies, hackers and crackers.
Protecting yourself from internet hoaxes, hackers and crackers, avoiding their misleading information, scams and phishing attacks.
In this guide, I will take you on a tour of 10 ways How Can You Protect Yourself From Internet Hoaxes.
What are Internet Hoaxes?
Internet Hoaxes are computer geek professional that is experts in spreading false and misleading Information that can be manipulated.
Internet hoaxes can spread fake news, compromised social media posts, spam emails, and altered images or videos.
They exploit people’s curiosity, emotions, or desire for sensational Information, leading them to share or engage with false content unknowingly.
The main feature or characteristic of internet hoaxes is the ability to spread rumors’ and false information quickly and make them viral.
To avoid internet hoaxes, users need to be equipped with critical thinking, some basic knowledge of information technology, and verifying and validating data | information.
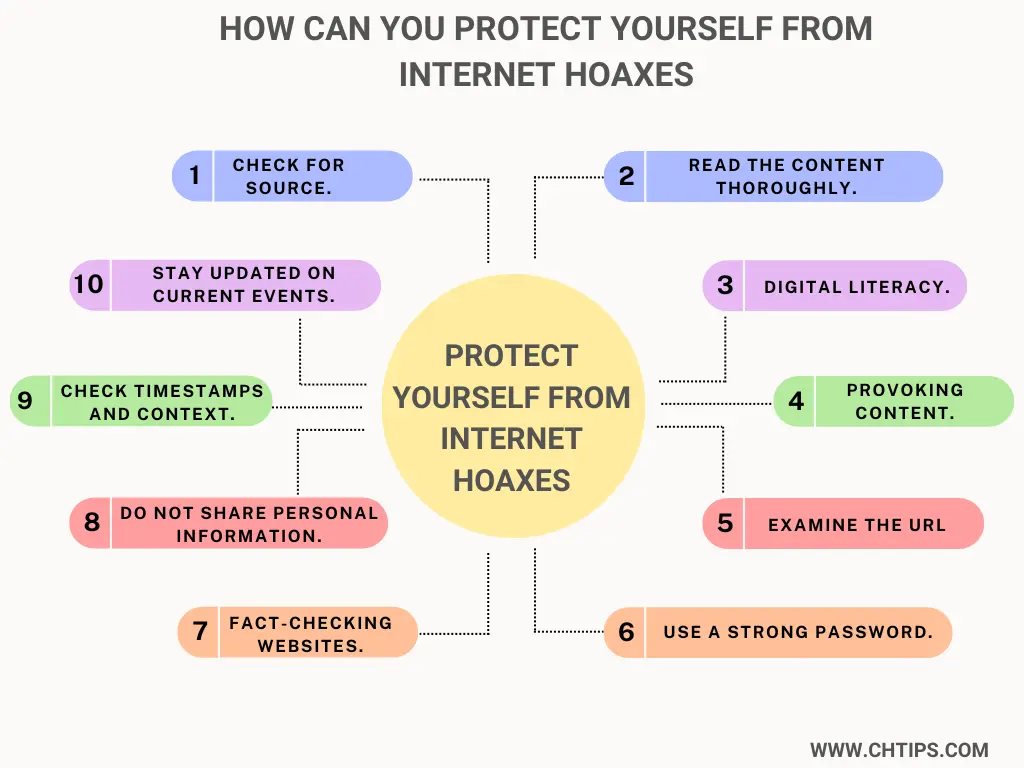
How Can You Protect Yourself From Internet Hoaxes
Internet Hoaxes can steal your sensitive Information using various methods online. To avoid such techniques, you should be digitally aware of the latest news, Information and trends.
Protecting yourself from internet hoaxes requires critical and logical thinking, with an additional layer of protection and caution when you consume Information online.
Below I have included some of the practical steps that can be used and utilized to avoid and Protect Yourself from Internet Hoaxes.
- Check For Source.
- Read the Content Thoroughly.
- Educate Yourself Related to IT | Digital Literacy.
- Click Bait Content | Provoking Content.
- Examine the URL For Suspicious Code.
- Use a Strong Password.
- Fact-Checking Websites.
- Do Not Share Personal Information.
- Check Timestamps and Context.
- Stay Updated on Current Events.
1. Check the Source.
Before accepting the Information or instruction available or served over the Internet to be true, you must recheck and validate before performing any actions.
You must check the origin of the Information, if it is from reputed, authenticated, official websites or trusted experts in the respective fields.
Other neutral sources should verify the credibility of the Information before accepting it to be true.
2. Read the Content Thoroughly.
The content, article or Information available over the Internet should be read thoroughly before concluding to a conclusion.
The Information can be misleading and deceptive; hence it is advised to follow this kind of Information only after rechecking.
It would help if you were sceptical of Information that is provoking and uses sensational language for convenience. Assessing the content with your logical reasoning to avoid further problems or inconvenience.
3. Educate Yourself Related to IT | Digital Literacy.
Digital literacy can cover evaluating, identifying, and analyzing the content and information server over the Internet.
Digital literate or digitally aware people can protect their personal and sensitive information, protect & maintain their online privacy and work safely in an online environment.
Online awareness gives the ability to differentiate between the legit and fraudulent Information available on the Internet. It also helps seamless communication, collaboration and careful engagement with other users online.
You must be aware of How you can protect Yourself from Internet Hoaxes by learning and making yourself aware of the method and techniques the internet hoaxes use and utilize.
You can stay informed by staying altered and updated.
- Common Internet Hoaxes.
- Scams.
- Misleading Information, data and content.
4. Click Bait Content | Provoking Content.
The social media post and blog posts are designed with attractive and clickbait headlines for more clicks and attention. This kind of content may produce harmful Information or malicious code or viruses that can harm your computer seriously.
Users are advised to be more cautious while engaging in this sort of content and consider rechecking or even avoiding sharing and promoting this sort of content.
5. Examine the URL For Suspicious Code.
Look closely at the website’s URL to detect any irregularities or imitations. Hoax websites may use similar URLs to established sources to trick readers. Check for misspellings, extra characters, or unfamiliar domain extensions.
6. Use Strong Password.
It would help if you created a strong password that is not easy to guess or crack; this is considered one of the crucial additional security measures to avoid inconvenience in the field of cyber security.
Let me include some tips in regard to creating strong passwords.
- Length.
- Use Uppercase and Lowercase.
- Use Special Symbols and Characters.
- Use numbers.
- Create Uniqueness.
It is advised for users to regularly and frequently change or update their passwords for more security. Now major websites and applications offer 2-factor authentication for an additional layer of security.
The second factor, authentication or verification, consists of fingerprints and one-time codes on mobile.
7. Fact Checking Websites.
The Internet is full of false and spam content. This information can damage and corrupt your thinking process and behavioural pattern.
You may have encountered such content that needs to be corrected but was still viral over the Internet. This happened because the user who shared this content did not bother to recheck, verify, or validate content reality.
Some websites offer services that can validate and check the accuracy of the Information presented by the websites or applications.
Snopes, fact checks, and PolitiFact are such examples.
8. Do Not Share Personal Information.
Computer systems can be compromised by malware and viruses. Hackers, Crackers, and Hoaxes try to trick the user by sending some malicious program using email or attachments.
This malicious program can be attached to images, videos, and text.
These programs can steal your sensitive, personal, and financial Information from your computer system. It would help if you were extra alert and cautious with personal Information sharing over the Internet.
9. Check Timestamps and Context.
Visual media like images, videos, and presentations can be manipulated to deceive users and trick them into sharing their personal and financial Information.
Therefore, you must check the timestamp and content over the Internet for its accuracy and authenticity,
10. Stay Updated on Current Events.
Keeping up with the latest news, content, articles, and events can help you identify hoaxes that may be circulating.
Be cautious of stories not covered by reputable news sources or lacking supporting evidence.
Social media platforms can be favourable grounds for misinformation. Spread awareness about internet hoaxes and help others become more discerning consumers of Information.
Applying and using these strategies and techniques gives you an upper hand over hoaxes and cyberbullies. Remember, Prevention is Better than Cure.
How Can You Protect Yourself From Internet Hoaxes Cyber Awareness 2023
Social media platforms can be play grounds for misinformation sharing.
Spread awareness about internet hoaxes and help others become more discerning consumers of Information.
| 1 | Stay Digitally Aware and Updated. |
| 2 | Aware of Phishing Attacks. |
| 3 | Validate and Verify Information Before Sharing. |
| 4 | Aware of Click Bait [Sensational Headlines]. |
| 5 | Make Yourself Digitally Ware about Hoaxes. |
| 6 | Use Legal Software and Applications to Fight Against Malware and Viruses. |
| 7 | Do Not Use Public WIFI. |
| 8 | Report and flag Suspicious Content. |
| 9 | Secure Account with Strong Passwords. |
Protect Yourself From Internet Hoaxes With the Help of Image
How Do I Protect Myself From Fake Websites?
In today’s internet world, protecting yourself from fake websites and application is almost mandatory.
To protect yourself, you need to be digitally illiterate and active, mixed with caution and awareness.
There are several key steps or techniques that should be used and utilized while accessing the Internet.
Before accessing any website, there are several points that need to be considered.
Such points, I have included them below.
- HTTPS [Hyper Text Transfer Protocol Secured] is mandatory for any website available over the Internet. HTTPS offers data and information encryption for an additional layer of security.
- The website’s legitimacy should be verified before performing personal and financial transactions.
- You must never click on suspicious links or email attachments from unknown sources. Pop Up Ads are malicious programs that can harm your computer, so avoiding them should be preferred.
- Use legal software that scans online websites and applications of malware and viruses.
- Regularly update the operating system and antivirus software for better and enhanced performance with security features.
- Before performing any financial transaction, you must consider user reviews regarding the product and company.
- Online Payment methods should be monitored and scrutinized.
What Types of Internet Fraud are Most Common?
There are several and numerous ways internet hoaxes try to cheat internet users. Some of such points are mentioned below.
- Phishing Attacks.
- Lottery Frauds.
- Online Credit Cards Scams.
- Discount Websites and Applications.
- Email and Online Shopping Frauds.
- Dating and Matrimony Scams.
- Online Auction and Classified Scams.
- Identity Theft.
- Employment Scams.
- Online Investment Scam.
What is a Common Indicator of a Phishing Attempt in Cyber Awareness 2023?
Common Indicators of a Phishing Attempt in Cyber Awareness 2023 are mentioned below.
- Suspicious Email Address.
- Controversial Language.
- Asking for Personal Information.
- Suspicious links or Attachments.
- Unsecured Connection.
- Stretching on Unusual Emergency and Urgency.
How Can You Protect Yourself from Social Engineering Cyber Awareness 2023
- Use Strong Passwords.
- Don’t Click on Unwanted or Suspicious Links.
- Do not Download from Unrecognized Sources.
- Enable Two-Factor Authentication (2FA).
- Sharing Content that Looks Suspicious.
- Avoid Sharing Personal Information.
- Verify and Validate Content and Information.
Recommended Reading
- Advantages and Disadvantages of Antivirus Software
- Data Protection for Websites in the Tech Domain
- Differences between HTTP and SMTP
- Advantages and Disadvantages of Gi-Fi
- What is a Computer Virus and Types
- 5 Functions of Software in Computer Systems
- Computer Basic Tutorials
Protect Yourself From Internet Hoaxes PDF Download
Useful Video: What are Internet Hoaxes | How to Avoid Them
Frequently Asked Questions [FAQs] On Protect Yourself From Internet Hoaxes
What are examples of malicious code?
How can we protect against malicious software?
2. Scan Your Computer Frequently for Viruses and Malware.
3. Do not Download from unauthorized sources.
4. Scan Twice Before Opening Emails.
5. Limit your file-sharing.
Four main types of malware?
What are the 3 pillars of security?
People, Processes, and Technology.
What are the 3 types of viruses?
2. File Viruses.
3. Boot Sector or Boot Record Viruses
What are 5 cyber safety rules?
2. Never Share Passwords and Sensitive Information.
3. Use Strong Passwords that are Difficult to Guess.
4. Update Your Password Regularly.
5. Use Different Password For Different Types.
Get In Touch
Users can protect themselves from internet hoaxes in today’s digital era.
Users must be digitally aware and literate to avoid inconvenience from internet hoaxes, cyber bullies and hackers.
Practicing skeptical thinking from unauthorized sources, verifying and validating sources, also performing safe internet behavior can significantly reduce the challenges faced by internet hoaxes.
I have also written and compiled some articles on computers and telecommunications, and please go through them.
I hope you will like reading it.
All the questions and queries related to the How Can You Protect Yourself from Internet Hoaxes | 15 Ways have been answered here.
If you have any questions about Protect Yourself from Internet Hoaxes Cyber Awareness 2023.
Don’t hesitate to contact me, and if you need to add, remove, or update anything from the article, please let me know in the comment section or via email.
I will be more than happy to update the article. I am always ready to correct myself.
I would like you to share this article with your friends and colleagues; this motivates me to write more on related topics.
!!! Thank You !!!